01_engage
1. You are performing reconnaissance for CEHORG and has been assigned a task to find out the physical location of one of their webservers hosting www.certifiedhacker.com. What are the GEO Coordinates of the webserver? Note: Provide answer as Latitude, Longitude. (Format: NN.NNN, *NN.NNN)
Ans: 37.751, -97.822
https://www.ipvoid.com/ip-geolocation/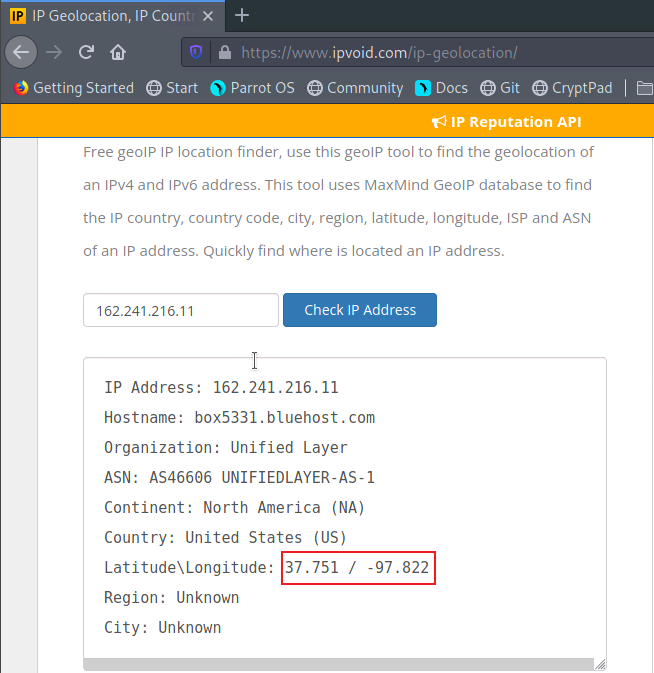
2. Identify if the website www.certifiedhacker.com allows DNS zone transfer. (Yes/No) (Format: Aa)
Ans: No
dig
dig NS www.certifiedhackr.com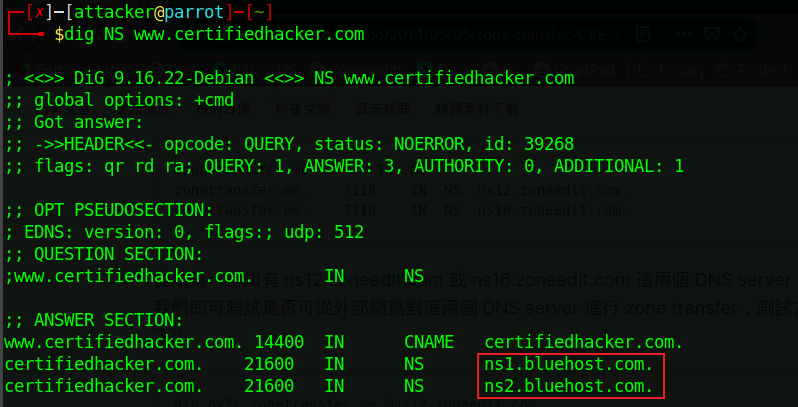
dig axfr www.certifiedhacker.com @ns1.bluehost.com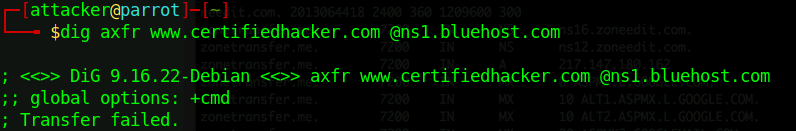
nslookup
nslookup -type=ns www.certifiedhacker.com
nslookup
server ns1.bluehost.com
ls -d www.certifiedhacker.com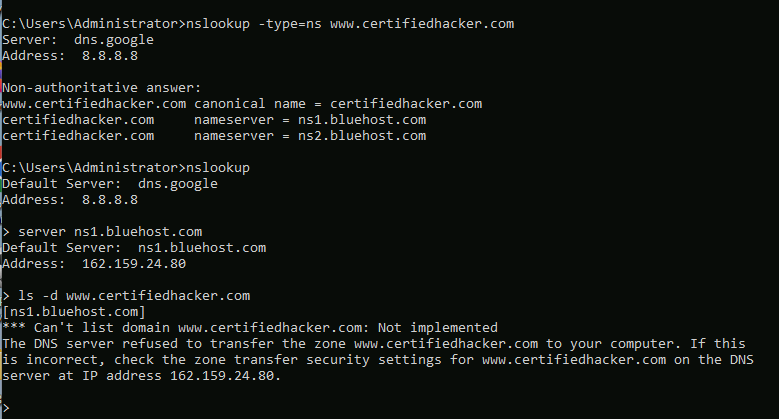
3. Identify the number of live machines in 172.16.0.0/24 subnet. (Format: N)
Ans: 3
nmap -sn 172.16.0.0/24 --min-rate=5000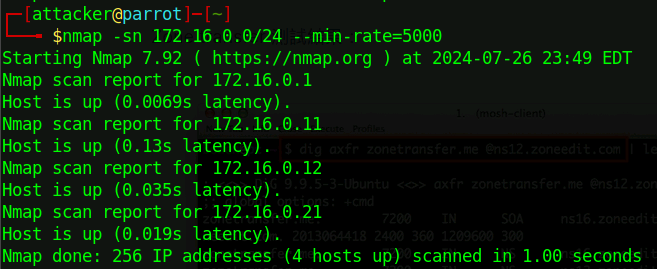
4. Find the IP address of the machine which has port 21 open. Note: Target network 172.16.0.0/24 (Format: NNN.NN.N.NN)
Ans: 172.16.0.12
nmap -p 21 172.16.0.11,12,21 --min-rate=5000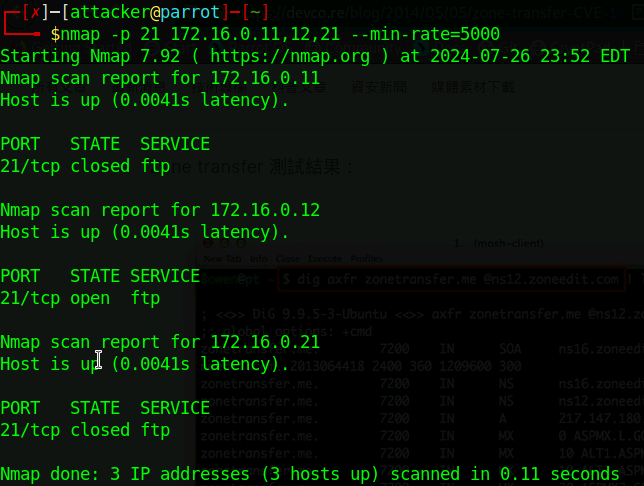
5. Find the IP address of the Domain Controller machine in 10.10.10.0/24. (Format: NN.NN.NN.NN)
Ans: 10.10.10.25
nmap -F 10.10.10.0/24 --min-rate=5000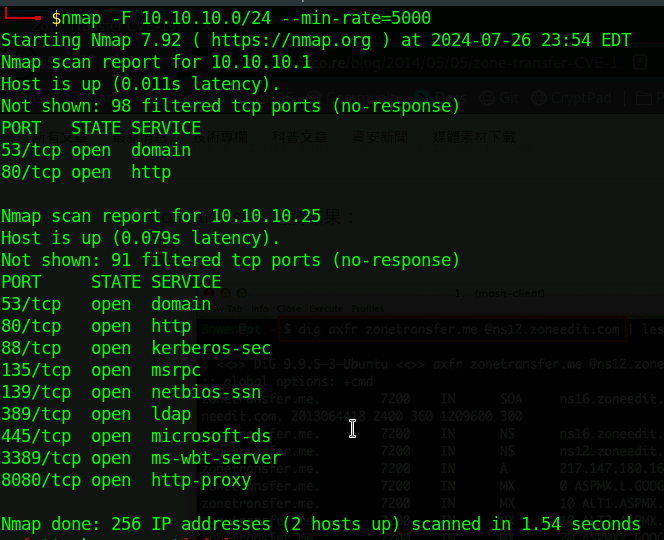
6. Perform a host discovery scanning and identify the NetBIOS name of the host at 10.10.10.25. (Format: AAAAAAAAA)
Ans: ADMINDEPT
nmap -p 445 -sC -sV 10.10.10.25 --min-rate=5000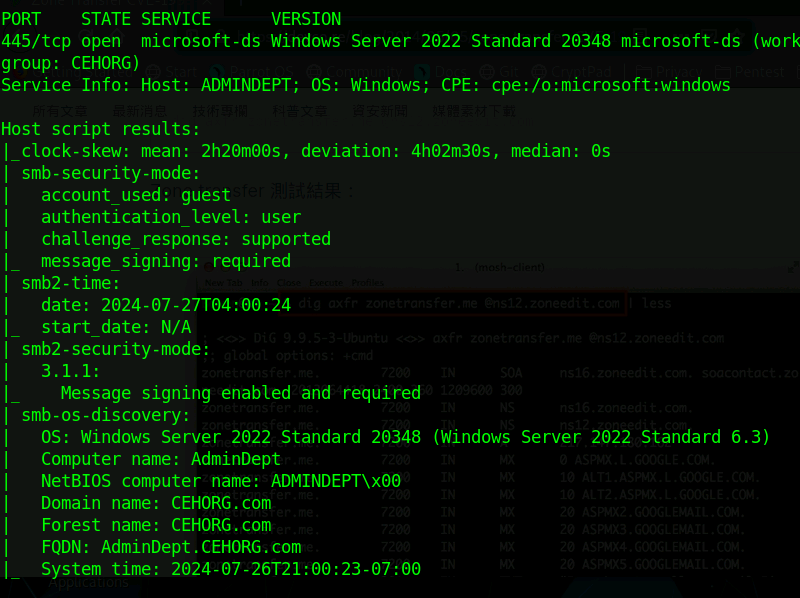
7. Perform an intense scan on 10.10.10.25 and find out the FQDN of the machine in the network. (Format: AaaaaAaaa.AAAAAA.aaa)
Ans: AdminDept.CEHORG.com
nmap -p 445 -sC -sV 10.10.10.25 --min-rate=5000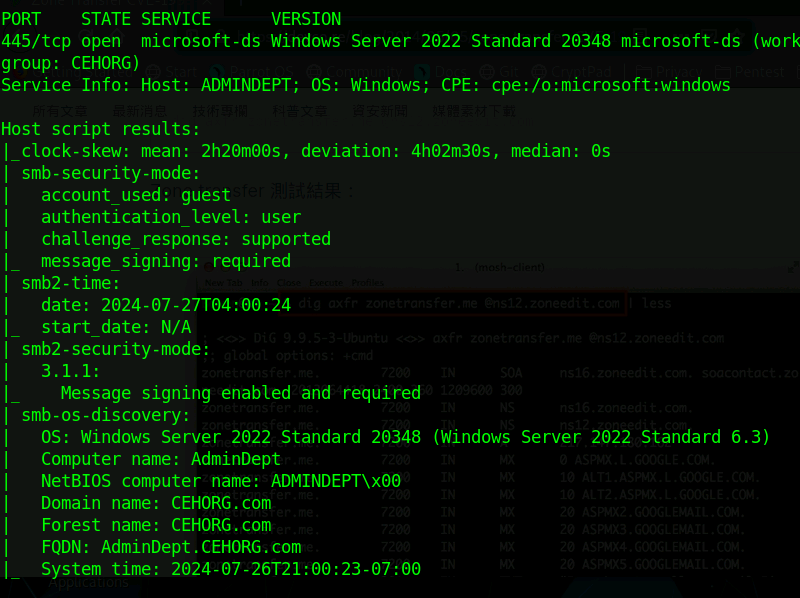
8. What is the DNS Computer Name of the Domain Controller? (Format: AaaaaAaaa.AAAAAA.aaa)
Ans: AdminDept.CEHORG.com
nmap -p 3389 -sC -sV 10.10.10.25 --min-rate=5000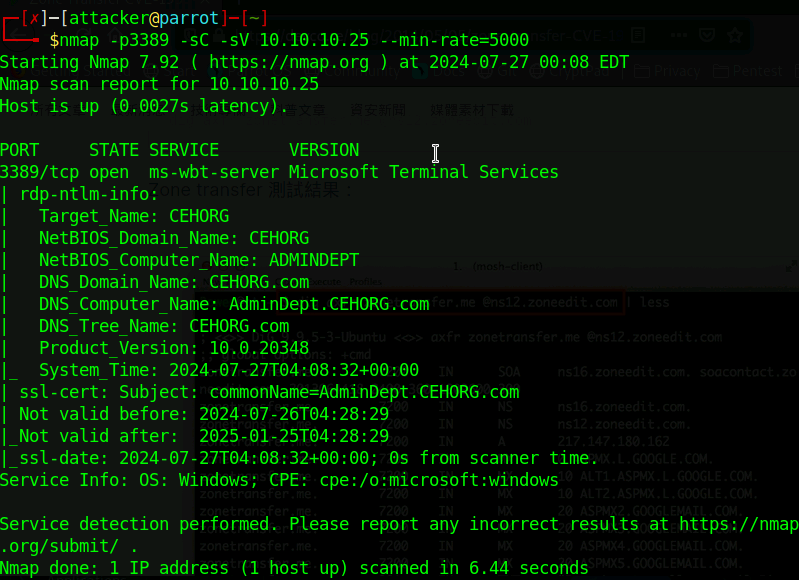
9. While performing a security assessment against the CEHORG network, you came to know that one machine in the network is running OpenSSH and is vulnerable. Identify the version of the OpenSSH running on the machine. Note: Target network 192.168.0.0/24. (Format: N.NaN)
Ans: 8.9p1
nmap -p 22 192.168.0.0/24 -sV --min-rate=5000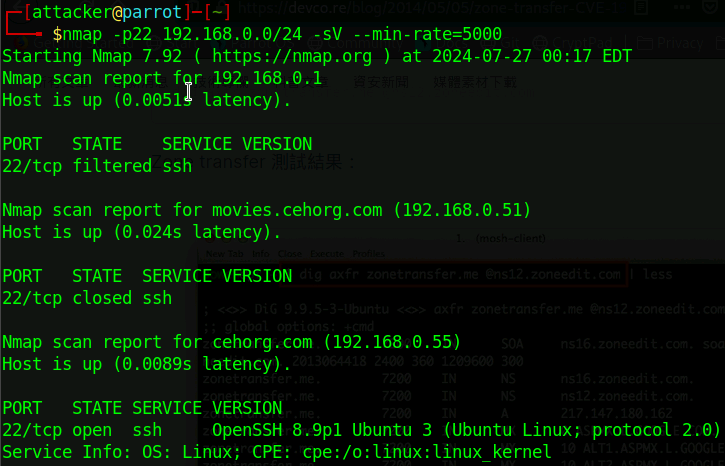
10. During a security assessment, it was found that a server was hosting a website that was susceptible to blind SQL injection attacks. Further investigation revealed that the underlying database management system of the site was MySQL. Determine the machine OS that hosted the database. (Format: Aaaaaa)
Ans: Ubuntu
nmap -F 192.168.0.51,55 --min-rate=5000 -sV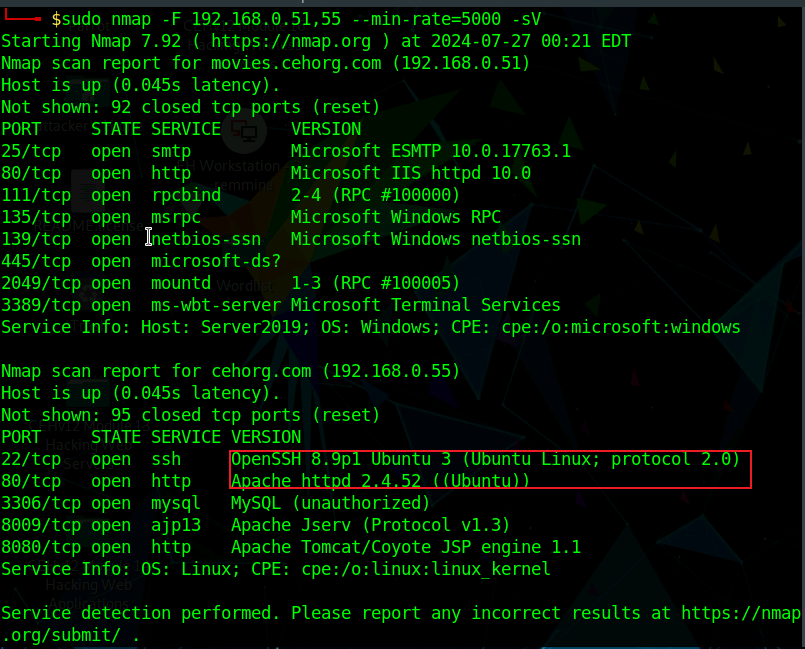
11. Perform LDAP enumeration on the target network and find out how many user accounts are associated with the domain. (Format: N)
Ans: 8
enum4linux
enum4linux -U 10.10.10.25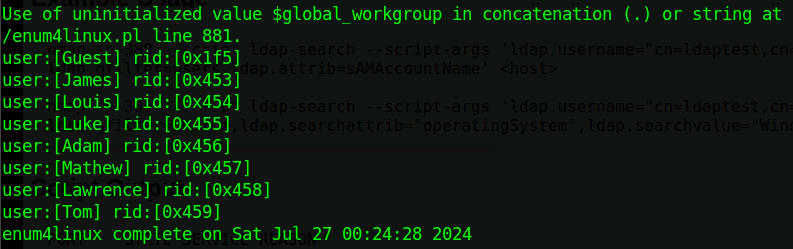
nmap
nmap -p 389 --script ldap-search --script-args 'ldap.username="dc=CEHORG,dc=com",ldap.password=,
ldap.qfilter=users,ldap.attrib=sAMAccountName' 10.10.10.25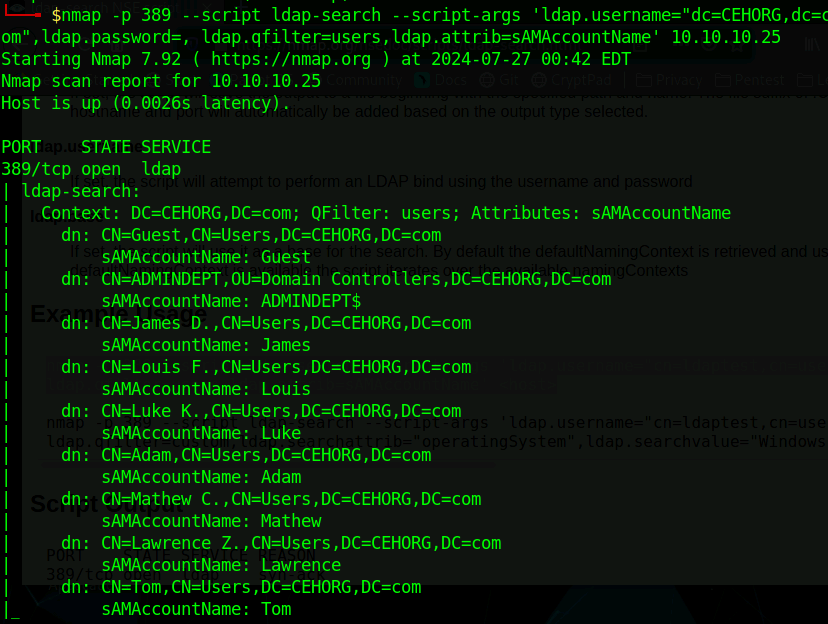
12. Perform an LDAP Search on the Domain Controller machine and find out the version of the LDAP protocol. (Format: AAAAaN)
Ans: LDAPv3
nmap -p389 -sV 10.10.10.25 --min-rate=5000 --script=ldap-rootdse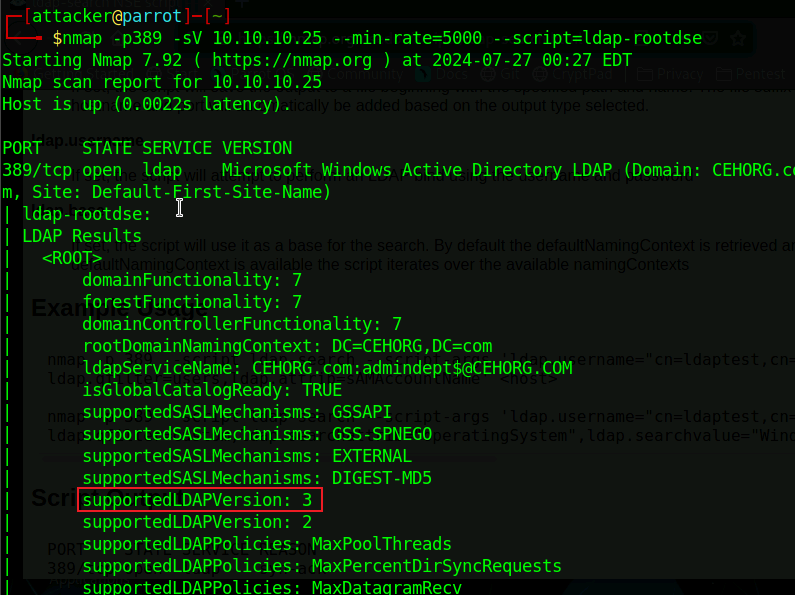
13. What is the IP address of the machine that has NFS service enabled? Note: Target network 192.168.0.0/24. (Format: NNN.NNN.N.NN)
Ans: 192.168.0.51
nmap -p111 192.168.0.51,55 --min-rate=5000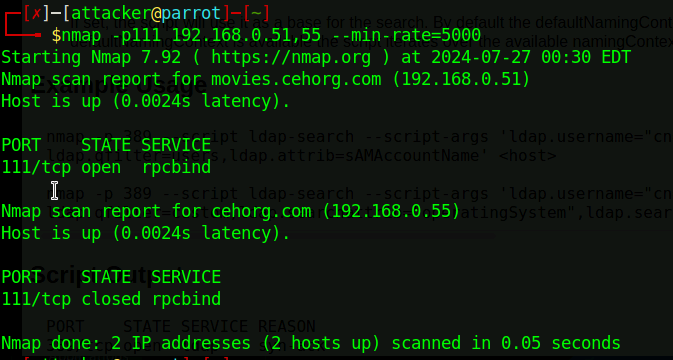
14. Perform a DNS enumeration on www.certifiedhacker.com and find out the name servers used by the domain. (Format: aaN.aaaaaaaa.aaa, aaN.aaaaaaaa.aaa)
Ans: ns1.bluehost.com, ns2.bluehost.com
dig ns www.certifiedjacker.com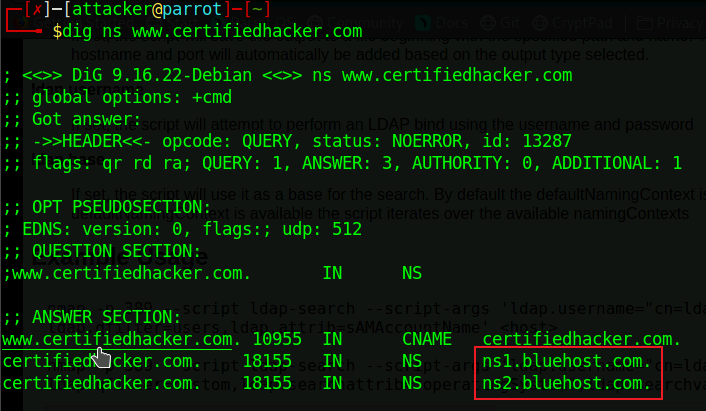
15. Find the IP address of the machine running SMTP service on the 192.168.0.0/24 network. (Format: NNN.NNN.N.NN)
Ans : 192.168.0.51
nmap -p25 192.168.0.0/24 --min-rate=5000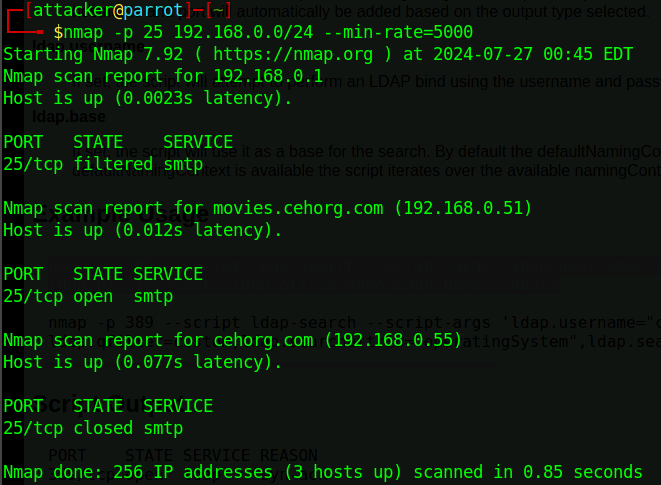
16. Perform an SMB Enumeration on 192.168.0.51 and check whether the Message signing feature is enabled or disabled. Give your response as Yes/No. (Format: Aaa)
Ans: Yes
nmap -p 445 -sC -sV 10.10.10.25 --min-rate=5000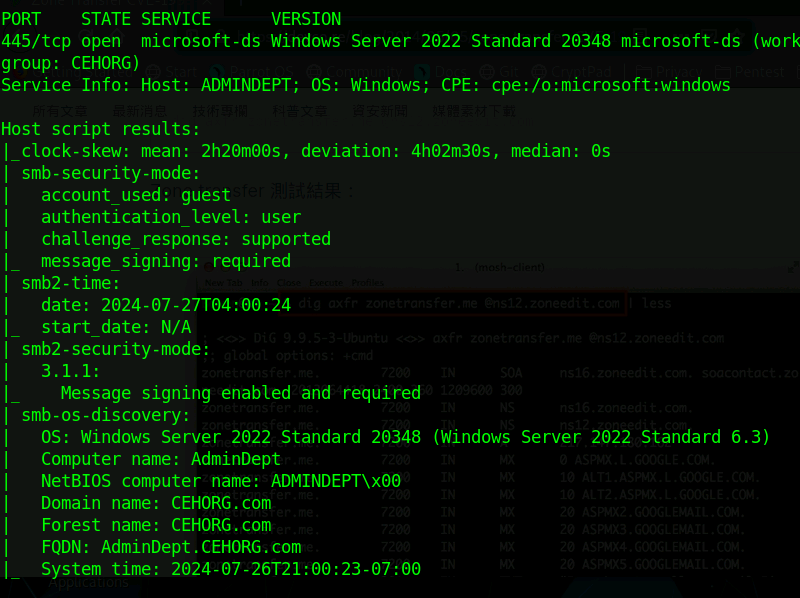
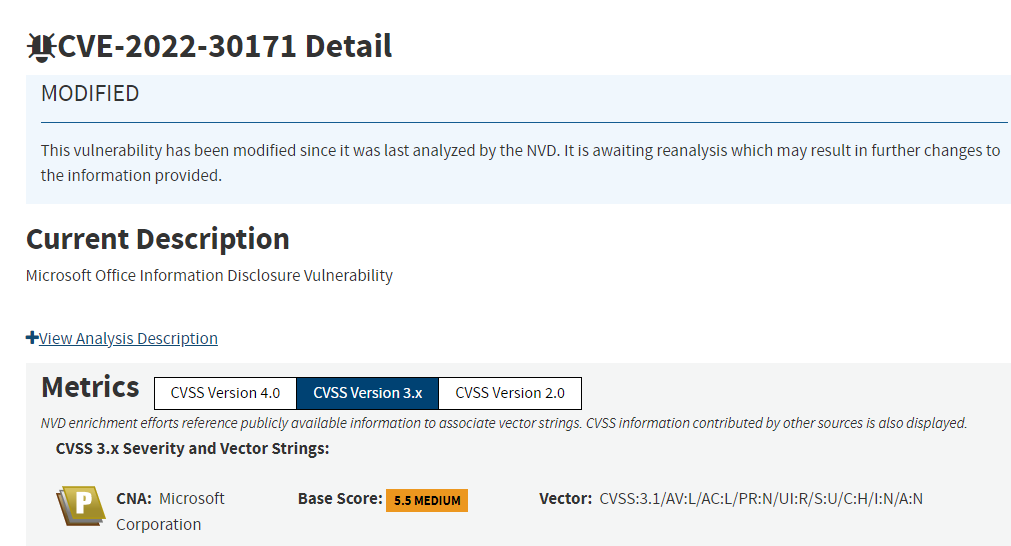
17. Perform a vulnerability research on CVE-2022-30171 and find out the base score and impact of the vulnerability. (Format: N.N Aaaaaa)
Ans: 5.5 Medium
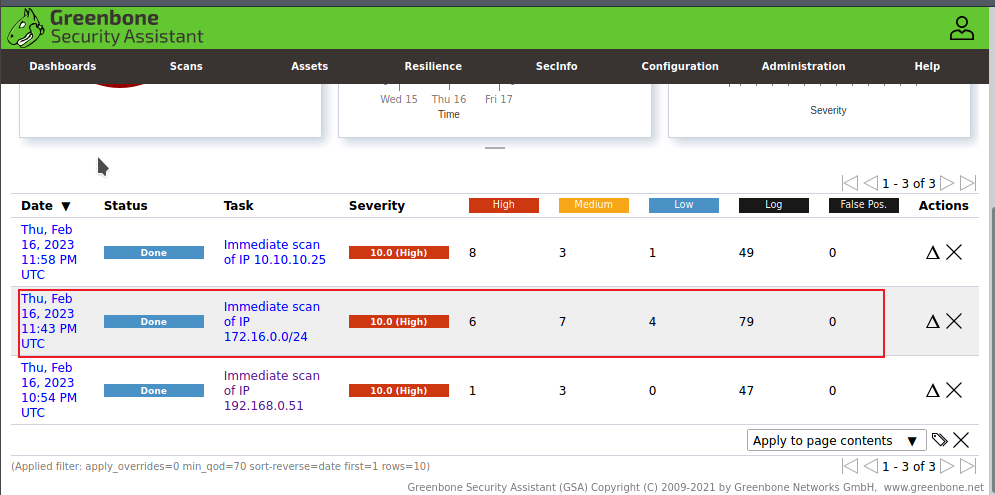
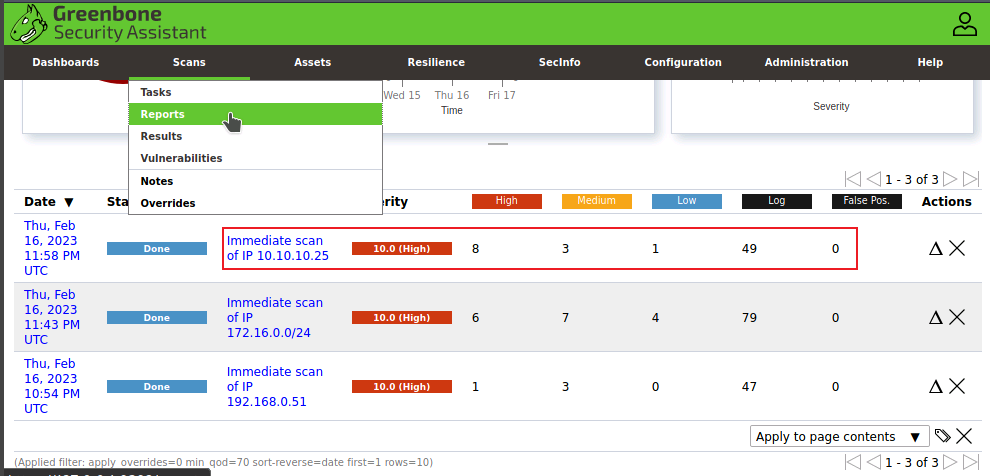
18. Perform vulnerability scanning for the domain controller using OpenVAS and identify the number of vulnerabilities with severity level as "medium". (Format: N)
Ans: 3
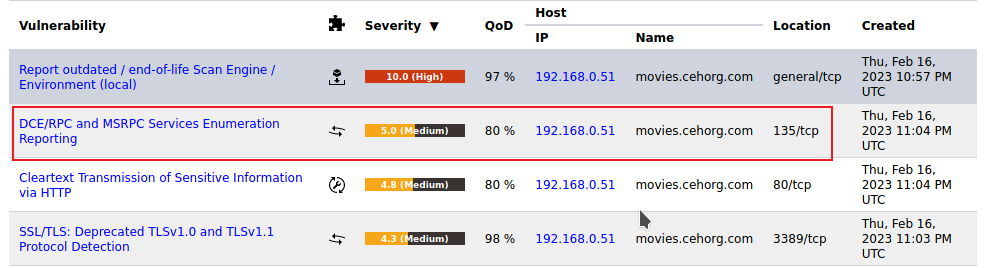
19. Perform vulnerability scanning for the webserver hosting movies.cehorg.com using OpenVAS and identify the severity level of RPC vulnerability. (Format: N)
Ans: 5
20. Perform vulnerability scanning for the Linux host in the 172.16.0.0/24 network using OpenVAS and find the number of vulnerabilities with severity level as medium. (Format: N)
Ans: 7